What is Security Architecture?
While there are various definitions of security architecture, it is ultimately a collection of security concepts, procedures, and models that balance opportunity and threat. Everything your business does creates the possibility of benefit and threats. You will have a different risk tolerance in different parts of your business. A good security architecture match with your benefit and risk objectives. Essentially ensuring you stay secure enough from cyber attacks. Business needs are translated into actionable security requirements through security architecture.
One way to immediately grasp it is to compare it to traditional architecture. The job of a security architect is quite similar to that of a house, school, or business building architect. They analyze the property, consider aspects such as customer preferences, soil type, terrain, and climate (the land's existing condition), and then devise a strategy to attain the desired result (the blueprint). Others construct the structure, in this case, builders and contractors, under the supervision of the architect to guarantee it achieves the goal (Architecture Governance).
The goal of most security architectures is to safeguard the enterprise against cyber threats. Security Architects will work with other Enterprise Architects in your business for a period in order to discover what makes your organization unique. They'll speak with your executives, staff, and business architects to learn about your company objectives, system requirements, consumer wants, and other essential aspects. They may then create a strategy and advice that is tailored to your company's goals and meets your stated cyber security risk appetite.
There are many enterprise architecture jobs on a leading enterprise architecture team. If you want to explore the roles, jump over to the different enterprise architecture jobs.

The Four Critical Elements of Security Architecture.
To better understand the nature of security architecture, it helps to see security architecture in four critical contexts.
There’s No Standalone Security Architecture
Let's One big component of security architecture is that there is no standalone security architecture. It is a ‘cross-cutting concern.’ That means that there is a security aspect to every enterprise architecture domain. For example: In the context of your business, when you think about your enterprise software, it will have a security component. That could be considered part of your security architecture and security operations.

The SABSA Model
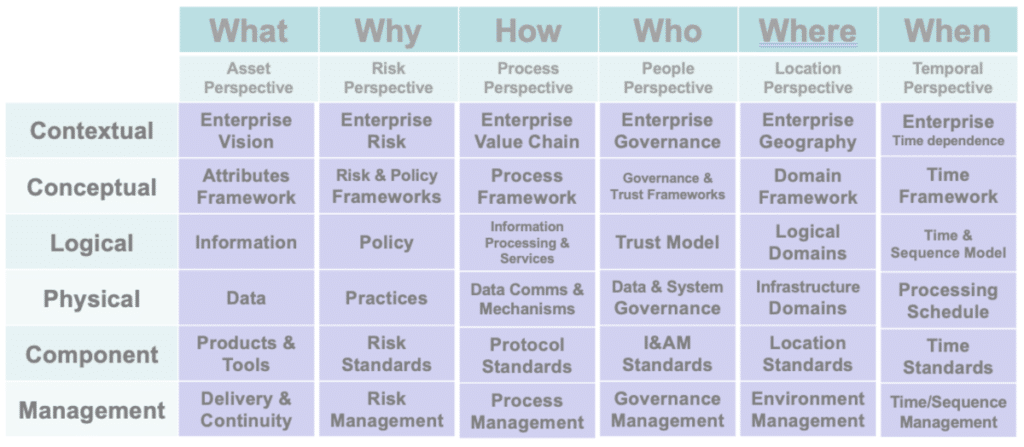
The best practice for security architecture is SABSA. SABSA is a risk-driven corporate information security architecture framework for supporting key business activities. While it is not directly related to the Zachman Framework, SABSA uses the core structure. The SABSA model's main feature is that everything must be drawn from a study of the business needs for security, particularly those in which security serves as an enabler for developing and exploiting new business prospects.
The process analyses the business demands from the start and develops a chain that is trackable through the strategy and concept, design, implementation, and continuous manage-and-measure phases of the lifecycle to ensure that the business mandate is maintained. The method is backed up with framework tools based on real-world experience.
The SABSA model is general in nature and may be used as a starting point for any organization; but, by going through the process of analysis and decision-making suggested by its structure, it becomes particular to the company and is eventually highly personalized to a specific business model. It becomes the enterprise security architecture, and it is critical to the organization's strategic information security management program's success.
The team at Conexiam has worked with The Open Group and the SABSA Institute to integrate the industry-standard EA framework, TOGAF, with SABSA. Download a copy of Integrating Risk & Security with Enterprise Architecture for more information.
It’s All About Risk Management
Security architecture is about risk management. Risk is the effect of uncertainty on meeting all of your business’s objectives. Uncertainty comes from missing an opportunity and being hit with potential threats. Security architecture does not necessarily result in protection against a threat. An element of risk management must be involved.
The practice of controlling risks linked with the use of information technology is known as information security risk management, or ISRM. It entails recognizing, analyzing, and responding to threats to an organization's assets' confidentiality, integrity, and availability. The final objective of this approach is to address risks in line with the risk tolerance of the company. Businesses should try to determine and take on an acceptable overall risk threshold for their firm, rather than expecting to remove all potential hazards.
Typically, risk management as part of security architecture will involve identifying assets, identifying potential vulnerabilities, identifying threats, finding controls, and conducting thorough assessments on a regular basis.
Security and Enterprise Architecture Need to Be Integrated
The development of Security Architecture needs to be fully integrated with the development of an enterprise architecture.
In most businesses, improving security is an impossible task. Rather than developing an integrated security architecture random work is performed to secure parts of the business. Often with other parts of the business subject to easy penetration or breach. Providing a secure environment requires preventative, investigative, and remedial measures.
Many conventional information security practitioners consider security architecture to be nothing more than the presence of security rules, controls, tools, and monitoring.
All security professionals should be aware of business objectives and strive to realize them by designing appropriate security controls that can be easily justified to stakeholders and related to the business risk. Enterprise frameworks, such as SABSA and the TOGAF Standard, aid in the alignment of security and business requirements.
Understanding TOGAF
TOGAF is an enterprise architecture framework. Enterprise Architects use the TOGAF Architecture Development Method (ADM) to focus change, reduce mistakes, and align IT with business divisions to create high-quality outcomes.
Have a look at our TOGAF vs. SABSA article to think of TOGAF plus SABSA. Extend your enterprise architecture with world-class risk and security.
Why Cyber Security Architecture is Important to an Organization
The first (and most evident) advantage of improved security is that security breaches are reduced. Many attackers employ extremely basic attack tactics that target common cybersecurity weaknesses that are shared by firms that aren't as engaged in developing a solid security architectural foundation.
Several distinct information security standards, such as HIPAA, GDPR, and others, are likely to apply to your company. Many of these data security standards demand that a company maintain a robust and well-managed security architecture, as well as a variety of particular security procedures. It's simpler to achieve these types of standards if you have a solid security architecture design as a key component of your organization. Having an accurate picture of your network architecture and the many security measures that are integrated, in particular, can make it simpler to determine whether you are in danger of breaking a major law.
Earning confidence requires a strong security architecture. When your company is acknowledged as a leader in the field of cybersecurity, it may help you gain the trust of others. This does not simply apply to potential clients; it also applies to possible business partners and potential partnerships that could happen in the future.
Next Steps: Security Architecture Training
This course is intended to provide a deeper understanding of Security Architecture. Learning is enhanced with hands-on experience through exercises based on real-world case studies.
The goal of the information systems security architect is to design controls that effectively manage risk associated with information and information technology. The goal of the security architect is to protect the enterprise, not the technology.
Effective security architectures are fully integrated with the architecture of the enterprise. Security architects must work with, not against, the tools, practices, and culture of the enterprise. They must balance the need to protect against the drive to succeed.
Key Security Architecture Learning Objectives:
On completing this course, students will be able to:
- Identify and assess business risks associated with information and information technology.
- Understand how to communicate risk.
- Describe the key information security concerns of confidentiality, integrity, and availability.
- Identify and describe the features found in typical information systems architectures, including networks, operating systems, and applications.
- Describe how security fits with architecture and systems development methodologies
- Identify and describe common security controls.
- Understand the connection between information systems security and privacy
- Comprehend the information systems security standards landscape.
- Define assurance and understand the role of assurance in information systems security.
- Identify and describe the top 20 information system safeguards.
Security Architecture Training Course
Included in the delivery:
- 3 days of instruction
- Lecture
- Workshop Exercises
- Exercise review
- Electronic copy of all Conexiam courseware and exercise materials
- Electronic copy of all Navigate templates and public architecture tools used in the course
- Students have access to up-dated courseware, exercise materials, Navigate templates and public architecture contents for over one year
All course material is provided electronically. For in-class delivery course slides and exercise materials are provided in a binder.
Recommended Prerequisites:
An understanding of systems or enterprise architecture. Completion of TOGAF Enterprise Architecture Training Course or EA with TOGAF® and Navigate™ is an asset.
Who Should Attend:
- Security engineers and designers who want to better understand the big picture
- Enterprise and system architects who want to understand security
For more information on Conexiam’s custom courses.