What is a Security Architect?
Ah, the ever-evolving world of cybersecurity. Enterprises, businesses, and organizations need professionals that are well-trained to keep their systems and processes safe 24-hours per day, 7 days out of the week.
Security architects work closely with enterprise architects when a new network is being created and developed. Instead of being focused on the organizational processes like an enterprise architect, Security architects are needed to keep a keen eye on network and application build. Together the network and applications are the sources of information security risk. Security architects make sure that the proper defensive measures are being emplaced right from the start.
An organization that sets up a network without careful consideration of proper security measures is almost sure to be on the receiving end of cyber security threats.
There’s a saying that goes something like, “security is the death of efficiency.” Well, it’s the security architect’s job to make sur that isn’t the case within an organization and network. This article sheds light on what a security architect is, and what that role means for an enterprise architecture team. If you want to explore the other roles, jump over to the different enterprise architecture jobs.
What Exactly Is a Security Architect?
Security architects are professionals at the management level who oversee an organization’s security network. The role of a security architect remains constant throughout all stages of the network processes; design, build, and implementation, as well as throughout the entirety of the network life.
Security architects also oversee any and all changes that are made to the respective network, so that the enterprise remains safe and free from security threats.
It’s quite common for security architects to both handle firewalls, anti-virus software, as well as offensive testing protocols, like penetration tests.
What is the different between CyberSecurity Architecture and Security Architecture
A cybersecurity architect is a specialist that focuses on protection from threats to information systems, whereas a security architect’s role is more aligned with risk management in a holistic sense. Now, that doesn’t mean the two roles are always mutually exclusive.
Cybersecurity specialization is often within the skillset of a security architect, but it’s important to understand the distinction. Due to its comprehensive nature, security architecture works well with the domain development process of enterprise architecture as a whole.
The Skillset of a Security Architect
While each enterprise and organization will have its own unique needs and skill requirements, the following is a list the general range of skills security architects should have:
Management Skills
Since this is a leadership role that has continuous oversight of processes, it’s paramount that security architects possess management skills. Security architects regularly managed multiple projects, as well as a team or teams of individuals in order to ensure network security is maintained.
Networking
Security architects play a significant part in the maintenance and building of various computer networks. Because of this, security architects need to have a comprehensive understanding of the principles of computer networking. For those that are considering pursuing a career as a security architect, this should be one of your primary focuses.
Malware Analysis
If you want to be effective as a security architect, you need to have a good general understanding of malware and malware analysis. Malware is something most businesses face and one of the most common threats to a network’s security.
Risk Management
A big part of the responsibility for a security architect, is risk management as a whole. This will be what cross-cuts into the fundamental enterprise architecture governance, and so understanding the fundamentals of risk architecture and risk management is critical.
What All Great Security Architects Have in Common
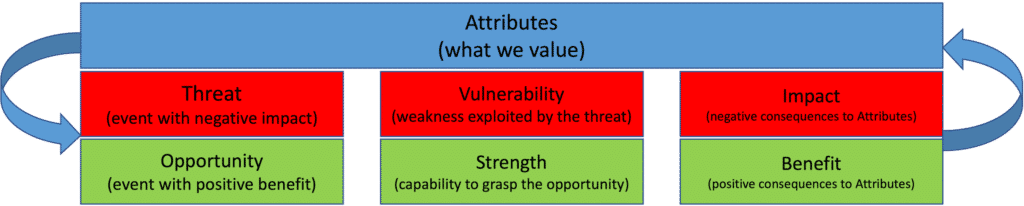
All of the top security architects across the board have all of the aforementioned skills, and then some. But what edges out “best from the rest” as they say, is the great security architects follow what’s known as SABSA's risk model.
SABSA is based on a comprehensive top-down model. The SABSA model drives the SABSA Development Process that develops the security architecture domain of your enterprise architecture. First, you understand the strategic context creating foundational business requirements. Step-by-step you extend the chain of traceability through the entire security architecture.
The basic questions are answered
- What is being considered?
- When is the activity performed?
- How is the activity performed?
- Who performs the activity?
- Where is the activity performed?
Asking the questions top-down ensures you have continually developed architecture specifications. For example, What at the Contextual Layer traces directly to What at the Component Layer.
SABSA's tools were built from practical experience, and work together. Some of the most important include the SABSA Model, the SABSA Business Attributes Profile, the SABSA Risk Model, and the SABSA Domain Model.
What Does a Security Architect Do?
Security architects are a major component of any IT project and initiative within a company or enterprise. They need to be there throughout every step of the process so they can aid in the designing, planning, and maintenance of the security architectures around these initiatives.
They work to optimize the levels of security throughout the whole organization, and run regular tests like vulnerability scanning, penetration testing, and risk analysis to ensure everything is protected.
What is The Role of a Security Architect in an Enterprise Architecture Team?
Enterprise architecture involves a wide array of digital processes, from authorization, identification, access controls, external authorization, and more. Every step of the way, security architects need to be cross-cutting every part of the enterprise’s processes, ensuring there aren’t any gaps in the security systems.

How Do You Become a Security Architect?
Preparation
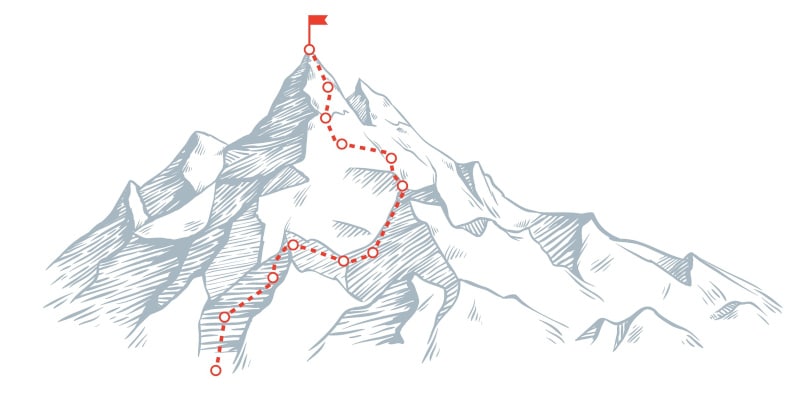
In a general sense, if you’re looking to pursue the role of security architect, you should know it’s not typically an entry-level position. Most security architects possess somewhere in the realm of 5-10 years’ experience, with at least a handful of those years focused in cybersecurity.
That means you’re going to need to be preparing for a long while if you want to get a chance at the role. Computer science degrees, as well as degrees focused on cybersecurity are all good starting points in this respective field.
Put together a personalized career plan so you know what steps you should be taking along the way, such as finding a position with some form of leadership responsibilities entailed.
Certifications
As with most high-paying cybersecurity positions, having the proper certifications do wonders for helping younger security professionals prove their talents, as well as standout from the competition. A good entry-level certification to start with is SABSA Foundation. SABSA Foundation will provide you with a clear understanding of Opportunity & Threat. Without understanding risk architecture and risk management is is easy to fall into the trap of security being the 'department of no.'
More advanced certifications that are good to acquire are CISSP, Certified Ethical Hacker (CEH), and Certified Cloud Security Professional (CCSP), among many others.
The more certifications you get, the better you’ll stand out in the crowd.
Continue Learning
Continuing your security and cybersecurity education is essential for a healthy career as a security architect. There aren’t many industries in the world that evolve and advance as fast as software technology, and security threats to networks adapt just as fast.
Continuous Learning needs to include both technical learning and what is often described as soft skills. Our free 12-week Architecture Kickstart includes training on serving stakeholders, understanding the problem, and critical thinking.
Taking a hiatus from security software can leave you behind to the point to where it’s difficult to catch up, and if you’re not already familiar with the interviewing process for software and cybersecurity positions, whiteboard interviews aren’t uncommon.
Custom Security Architecture Training
This course is intended to provide a deeper understanding of Security Architecture. Learning is enhanced with hands-on experience through exercises based on real-world case studies.
The goal of the information systems security architect is to design controls that effectively manage risk associated with information and information technology. The goal of the security architect is to protect the enterprise not the technology.
Effective security architectures are fully integrated with the architecture of the enterprise. Security architects must work with, not against, the tools, practices, and culture of the enterprise. They must balance the need to protect against the drive to succeed.
Security Architecture Training Key Learning Objectives:
On completing this course, students will be able to:
- Identify and assess business risks associated with information and information technology.
- Understand how to communicate risk.
- Describe the key information security concerns of confidentiality, integrity, and availability.
- Identify and describe the features found in typical information systems architectures including networks, operating systems, and applications.
- Describe how security fits with architecture and systems development methodologies
- Identify and describe common security controls.
- Understand the connection between information systems security and privacy
- Comprehend the information systems security standards landscape.
- Define assurance and understand the role of assurance in information systems security.
- Identify and describe the top 20 information system safeguards.
Security Architecture Training Course
Included in the delivery:
- 3 days of instruction
- Lecture
- Workshop Exercises
- Exercise review
- Electronic copy of all Conexiam courseware and exercise materials
- Electronic copy of all Navigate templates and public architecture tools used in the course
- Students have access to up-dated courseware, exercise materials, Navigate templates and public architecture contents for over one year.
Recommended Prerequisites:
An understanding of systems or enterprise architecture. Completion of TOGAF® 9 Certification or EA with TOGAF® and Navigate™ is an asset.
Who Should Attend:
- Security engineers and designers who want to better understand the big picture
- Enterprise and system architects who want to understand security
Purchase the Security Architecture Course
The Security Architecture class is sold as a custom course for your organization. Contact sales@conexiam.com or Contact Conexiam. For more information on Conexiam’s custom courses.
How Do You Become a Security Architect?
Security architects are critical for a healthy, safeguarded business to function on a day-to-day business. One malicious attack and mean the end of an organization, whether it be holding their data hostage, compromising accounts, or erasing databases.
That means there’s a lot of responsibility on the shoulders of security architects, but it’s also a very rewarding, lucrative position that is known to provide great job satisfaction.
Ready to start your journey on becoming a security architect? Conexiam has put together some of the most comprehensive integrations, that provide enormous benefit for enterprises and those interested in becoming security architects.
Our TOGAF and SASBA Integration offers best practice risk management in the TOGAF Standard, enhances TOGAF architecture requirements with SABSA's Business Attributes Profile, as well as sheds light on where to develop security architecture information in the TOGAF ADM.
We’ve also got a comprehensive standard Integrating Risk and Security with TOGAF guide that provides a wealth of information on risk management, as well as SABSA best practices.
At Conexiam, we’re a boutique shop with experience in multiple industry verticals across the US, Canada, Africa and the Middle East. Conexiam has established a sound practice of developing architecture predictably.
Understanding the purpose of the architecture engagement, and what information they require, allows Conexiam to tailor the architecture deliverables. Conexiam has developed a Predictable EA approach using fixed periods of time with known deliverables and work product.
Do it Yourself Path to Becoming a Better Security Architect
Complete guidance for best practice enterprise security architecture and enterprise risk management
Industry Standard EA Capability Reference Model
Learn the basics of best practice enterprise security architecture based on balancing Opportunity & Threat
Increase your understanding of who benefits from an upside and who carries the downside. Use SABSA Domain Modelling.
Examples of Successful Security Architects
Best practice Security Architecture optimized the upside and minimizes the downside. Threat & Opportunity. Balance your risk!


